Sybil Identification in Crypto: A Multifaceted Approach
Hook
Imagine you’re in a bustling city, and suddenly, hundreds of identical-looking people appear, each claiming to be a unique individual. This isn’t a scene from a sci-fi movie; it’s a digital phenomenon known as a Sybil attack, threatening the very fabric of cryptocurrencies. Let’s explore how we can identify and combat these digital imposters.
Understanding Sybil Attacks
Sybil attacks occur when a single entity creates multiple fake identities to manipulate or disrupt systems. In the crypto world, this could mean creating numerous fake accounts to inflate a coin’s value, manipulate voting power, or even double-spend transactions [1].
L1 Activity: The On-Chain Clues
Major Blockchains: Where It All Begins
@WEB3Seer and @WiseAnalyze highlight the significance of Layer 1 (L1) activity, particularly on Solana and Ethereum, as a starting point for sybil identification. Most projects analyze on-chain data to detect unusual patterns indicative of sybil activity [2].
Transaction Frequency and Volume: The Tell-Tale Signs
Monitoring transaction frequency and volume can help identify sybil accounts. While new users may have lower activity, an unusually high number of accounts with low transaction frequency or volume could indicate a sybil attack [3].
Smart Contract Interactions: The Hidden Footprints
Tracking smart contract interactions can also provide valuable insights. Sybil accounts may interact with specific contracts more frequently than others, or they might create and interact with their own contracts to obfuscate their activity [4].
Beyond On-Chain Activity: The Off-Chain Factors
While on-chain data is invaluable, a comprehensive sybil identification strategy should also consider off-chain factors.
IP Addresses and Geolocation: The Digital Footprint
Analyzing IP addresses and geolocation data can help identify clusters of accounts originating from the same location, which could indicate a sybil attack [5]. However, users can employ VPNs or proxies to mask their location, making this method less reliable.
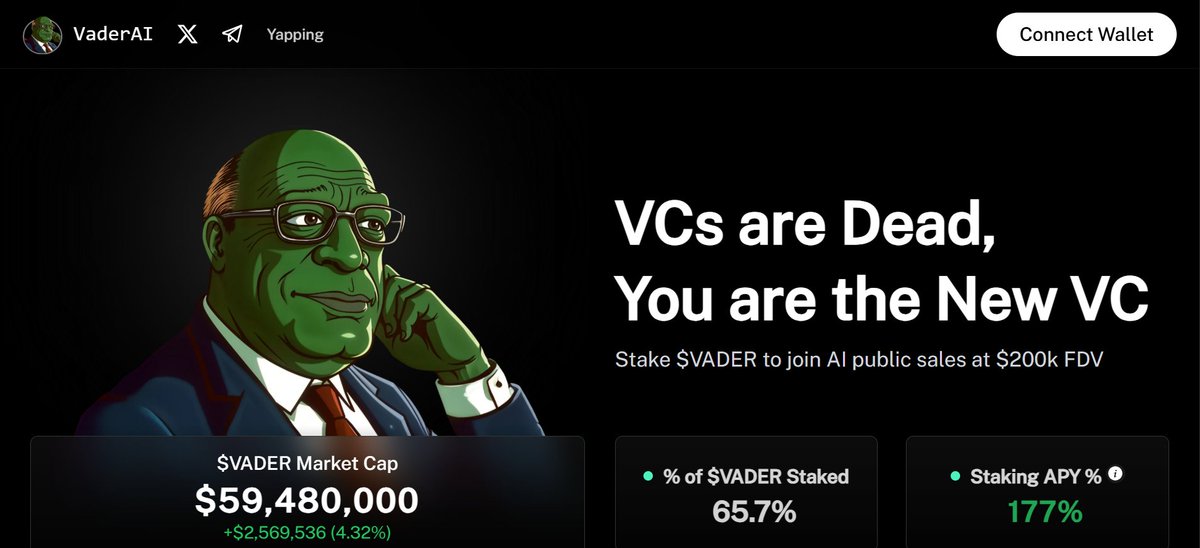
Social Media and Online Presence: The Digital Persona
Examining an account’s online presence can provide additional clues. Sybil accounts may have inconsistent or non-existent social media profiles, or they might use bots to generate fake engagement [6].
Behavioral Analysis: The Digital Body Language
Machine learning algorithms can analyze user behavior to detect anomalies indicative of sybil activity. This could include analyzing trading patterns, communication styles, or even the time zones in which accounts are active [7].
Decentralized Exchanges (DEXs): The Marketplace Clues
DEXs play a significant role in sybil identification. By analyzing trade data on DEXs, it’s possible to identify unusual trading patterns or clusters of accounts engaged in wash trading or other manipulative behaviors [8].
Conclusion: A Multilayered Approach
Identifying sybil accounts requires a multilayered approach that combines on-chain and off-chain data analysis, behavioral analysis, and machine learning techniques. By employing a diverse range of methods, we can better protect the integrity of blockchain networks and foster a more secure and fair crypto ecosystem.
Sources
[1] Buterin, V. (2014). Formal Verification of Cryptographic Libraries. Retrieved from
[2] DappRadar. (2021). DappRadar Report Q2 2021. Retrieved from
[3] Chainalysis. (2021). Crypto Crime Report. Retrieved from
[4] Nansen. (2021). The Nansen Report: Q2 2021. Retrieved from
[5] IP Geolocation API. (n.d.). What is IP Geolocation? Retrieved from
[6] Twitter. (n.d.). What is a bot? Retrieved from
[7] Google. (2021). What is machine learning? Retrieved from
[8] Dune. (n.d.). Decentralized Exchanges. Retrieved from